This is a growing issue of automated traffic on the web. It does not leave much legroom for any spike or genuine attacks.
The past few months I’ve been helping clients mitigate this. As far as DDoS it must be really targeted because between services like Cloudflare and data center’s with built in mitigation, it’s not a common or long-lasting thing these days.
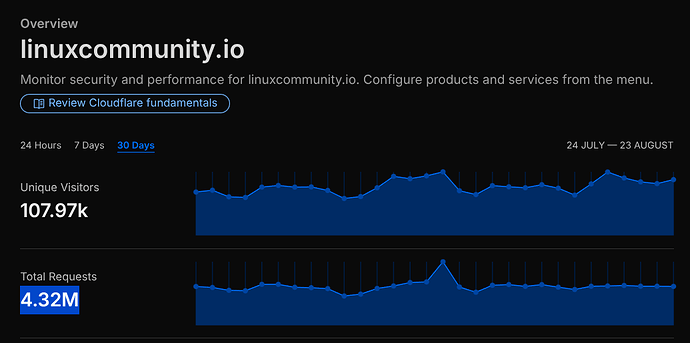
To give you an idea, here are the edge stats from Cloudflare WAF that sits in front of our forums:
Of the 108k “unique visitors,” 100k were non-human. ![]() And a whopping 4 million requests most of which mitigated by firewall rules. If it weren’t for their WAF, I’m sure the forums would have been largely unavailable or slower. (The specs of this VM is lower than an iPhone lol)
And a whopping 4 million requests most of which mitigated by firewall rules. If it weren’t for their WAF, I’m sure the forums would have been largely unavailable or slower. (The specs of this VM is lower than an iPhone lol)
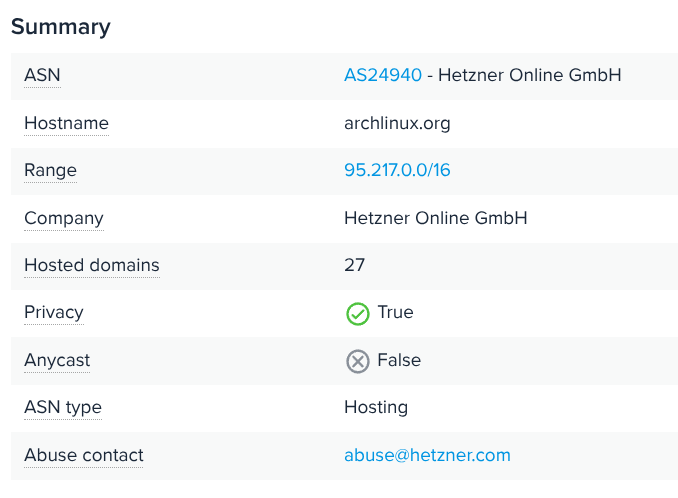
A quick check and archlinux.org does not have a proxy/firewall in place (unless they are using a custom server in front of their HTTP server). The IP is exposed, is showing regular hosting:
Hosted by Hetzner which is a good hosting company. However, often DDoS its only so much hosting companies will invest in it. It’s going to be Arch’s responsibility to mitigate.
The internet is fast becoming an environment where self-hosting anything more than a hobby-site requires serious consideration about automated traffic, targeted and non-targeted scanning, flooding, and DDoS.